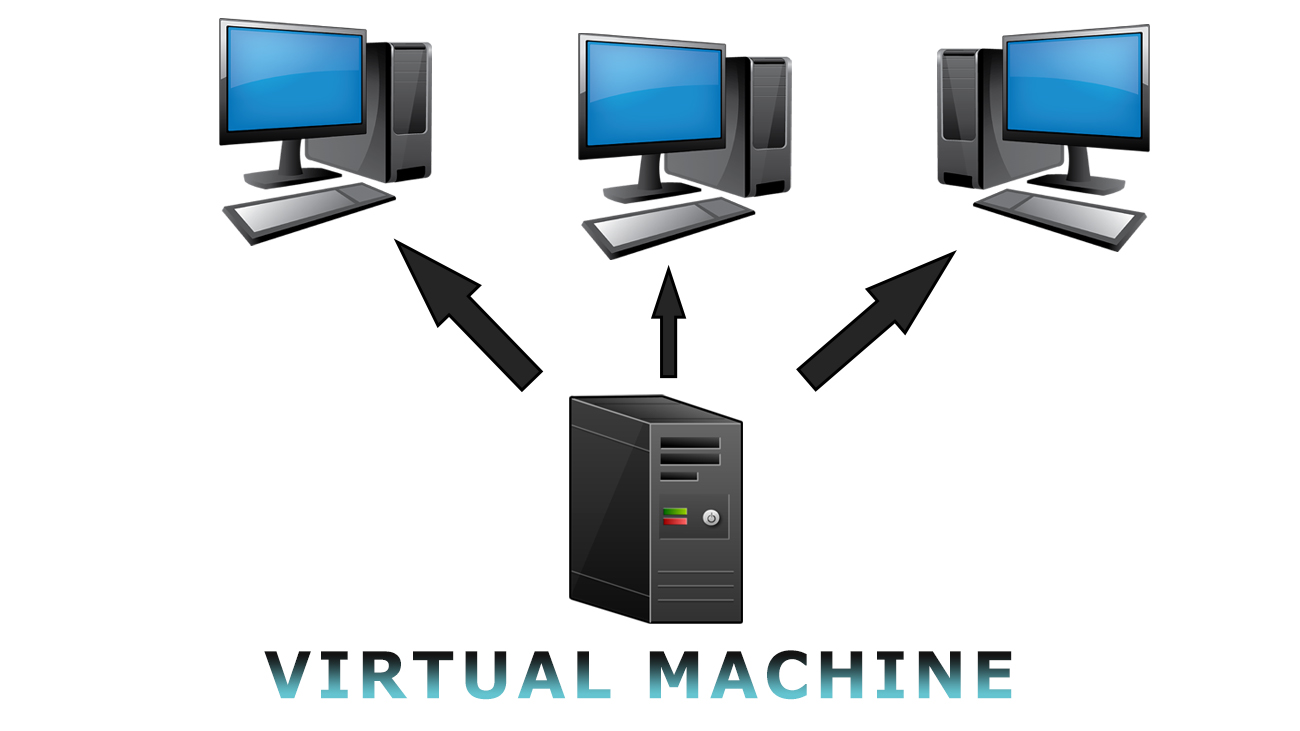
A virtual machine is commonly known as VM, which behaves like a separate computer system. These are open-source applications that can be installed in any operating system. The virtual machine acts as a separate physical computer with different operating systems that we like to install (Ex: Windows, Linux, Ubuntu, macOS, etc..)
There are various virtual machines, some of the famous VM's are
- VirtualBox
- VMware
- Boot camp
- VMware Fusion (Mac)
- VM Monitor
What are VMs used for?
Trying out a new operating system (OS), including beta releases.
Running software or apps on operating systems that they were not originally intended for.
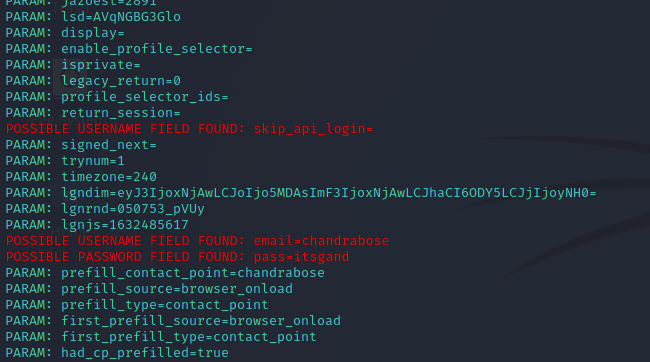
Used in cybersecurity
Some benefits of using VMs?
Cost savings
Security benefits
Run multiple Operating Systems